The iBook G4: the network that vanished
In an earlier piece, I described the iBook G4 as a machine that waited. Its pace is deliberate, its expectations modest, its presence patient. Much of that waiting once happened across the network: login windows opening, contact lists refreshing, conversations beginning somewhere beyond the edge of the screen. The machine still performs those gestures today. What has changed is the network that once answered them.
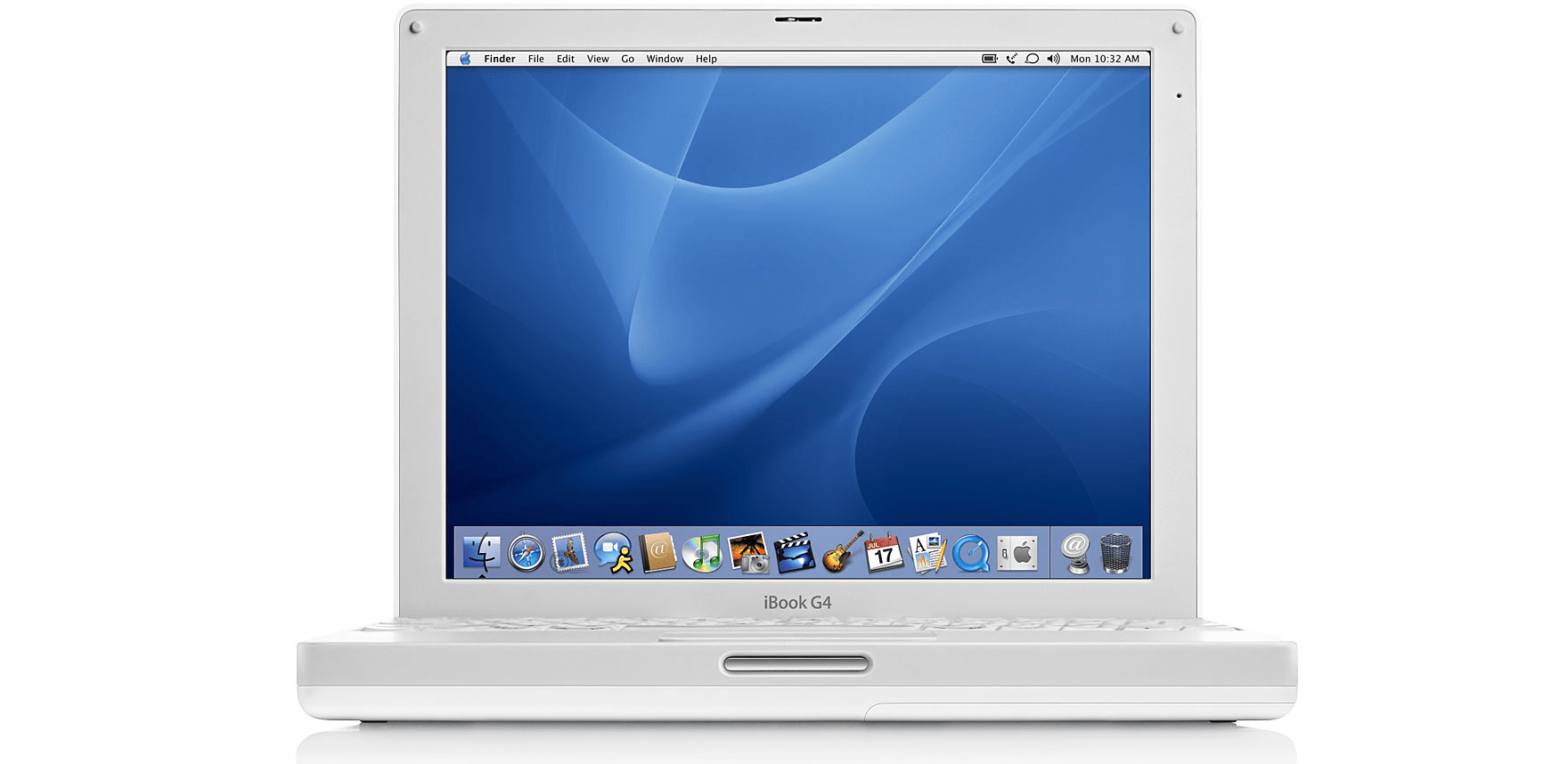
Opening the Applications folder reveals a small constellation of programs that once mediated daily presence on the early internet. Their icons remain unchanged: Skype, MSN Messenger, ICQ, Twitterrific, Vuze. Each launches without hesitation. Windows appear, menus respond, preferences load exactly as they did two decades ago. The software itself has survived intact, preserved within the boundaries of the PowerPC ecosystem.
What has not survived is the network they expected to find.
The login dialogs still invite authentication. Contact lists attempt to refresh. Status indicators search quietly for servers that no longer answer. In 2006 these programs were gateways to people and conversations, to communities that seemed as stable as the operating system itself. Today they open into silence. The binaries remain functional, but the infrastructures that sustained them have dissolved, leaving behind interfaces designed for a world that no longer exists.
In this sense, the iBook reveals a peculiar asymmetry. Hardware ages slowly. Software can endure indefinitely if preserved. Digital ecosystems, by contrast, are often fragile constructions, dependent on servers, companies, and protocols whose lifespans may be measured in years rather than decades. A computer like the iBook can remain operational long after the networks it once inhabited have faded away. The machine persists, patiently ready to connect, while the network it remembers has already vanished.
Protocols that once felt permanent
In the early 2000s, the online world appeared structured around a set of relatively stable communication protocols and services. Instant messaging platforms formed the backbone of everyday interaction. ICQ numbers were exchanged as naturally as phone numbers. MSN Messenger windows opened automatically after login, populating the screen with familiar usernames and green status indicators. Early Skype clients established peer-to-peer voice connections that felt almost miraculous in their simplicity: install the software, add a contact, and speak.
These systems felt infrastructural rather than temporary. They persisted year after year with minimal visible change, creating the impression that the networks themselves were permanent. Contact lists accumulated gradually, becoming quiet records of friendships, classmates, collaborators, and acquaintances encountered across different periods of life.
Looking back, the architecture of those networks was comparatively simple. Many services relied on lightweight protocols, modest server infrastructure, and client software that ran locally on personal machines. Conversations were handled by dedicated applications rather than integrated into web browsers or mobile platforms. The internet felt composed of many small systems, each performing a specific function and communicating through clearly defined interfaces.
On the iBook, that earlier structure is still visible.
The clients remain exactly where they were installed. Opening Skype reveals a familiar interface designed for a world where peer-to-peer voice communication was still novel. ICQ opens to a login window that expects a numerical identifier rather than an email address. MSN Messenger displays the carefully designed contact list interface that once defined online presence for an entire generation of users.
Launching these clients today reveals how fragile the underlying networks were.
ICQ’s original infrastructure has long since been retired. MSN Messenger’s network was absorbed and eventually discontinued. Early Skype clients can still render their login screens, but authentication fails against modern servers. Twitterrific’s early versions attempt to contact APIs that no longer exist. Even BitTorrent clients such as Vuze open to tracker lists whose original hosts have disappeared or migrated elsewhere.
What remains is the interface: windows carefully designed to manage conversations that can no longer begin.
The software waits for responses from systems that have quietly ceased operation.
Interfaces without conversations
The experience of launching these applications today produces a subtle but distinctive effect. Unlike corrupted software or incompatible binaries, these programs appear perfectly healthy. Their interfaces render cleanly. Buttons respond immediately. Preferences panels open exactly as expected. Nothing within the software itself suggests that anything is wrong.
The failure occurs elsewhere.
Login attempts time out. Contact lists remain empty. Status indicators never change from their initial state. The applications behave as though they are waiting for replies that will arrive eventually.
Technically, many of these failures result from predictable changes. Authentication servers have been shut down. Encryption protocols have evolved beyond what older clients can support. APIs have been redesigned or removed entirely. Domain names once associated with these services now point to unrelated systems or simply return no response.
From a software engineering perspective, the situation is understandable. Network services evolve rapidly. Maintaining backward compatibility indefinitely is rarely practical. Infrastructure must adapt to changing security models, new hardware architectures, and shifting patterns of use.
Yet the result, when viewed from the perspective of preserved hardware, is striking.
The iBook still contains fully functional programs designed to interact with networks that no longer exist.
Opening them feels less like running software and more like examining instruments from an earlier technological environment. Their interfaces describe a world that once operated according to a different set of assumptions about identity, communication, and online presence.
In that world, contact lists were local records stored on personal machines. Conversations occurred through dedicated applications rather than unified platforms. Services competed through protocol design and client experience rather than through the scale of centralized ecosystems.
Those assumptions shaped the software that still resides on the iBook.
Survivors and fragments
Not every network from that era has disappeared entirely. Some systems continue to exist precisely because they were built on decentralized principles.
IRC networks, for example, still operate much as they did decades ago. Independent servers maintain channels dedicated to technical communities, open-source projects, and niche interests. BitTorrent remains functional as well, sustained by distributed trackers and peer-to-peer data exchange. Multiplayer games from the same period can often be revived through private servers or local network play.
These survivors share a common characteristic: they do not depend on a single organization or infrastructure provider. Their protocols allow networks to persist even as individual servers appear or disappear.
The contrast with the earlier messaging platforms is instructive. Services such as MSN Messenger or ICQ depended heavily on centralized infrastructure controlled by a single company. When those systems were retired, the entire network effectively vanished overnight.
The iBook preserves evidence of both models. Some programs still connect successfully to the wider internet, albeit slowly and with certain limitations. Others remain permanently disconnected, their functionality reduced to a static representation of what once occurred through them.
A machine that remembers
Returning to the iBook after exploring these programs leaves an unusual impression. The computer itself is stable, responsive, and entirely usable within the limits of its architecture. Mac OS X Leopard launches applications quickly from the SSD. The PowerPC G4 continues to execute instructions with the same predictable rhythm it had in 2006. Nothing inside the machine suggests failure or decay.
What has changed exists outside the hardware.
The networks that once animated these programs have been replaced, consolidated, or abandoned. Protocols gave way to platforms, and platforms eventually gave way to newer systems built on different assumptions about identity, presence, and communication. The software on the iBook still reflects the earlier structure of the internet: a landscape of independent services accessed through lightweight clients running locally on personal machines.
Opening those clients today reveals only the outline of that landscape. The paths remain visible, but the destinations have faded.
Time
When the iBook connects to the internet, it still synchronizes its clock using NTP servers. Time itself still flows across the network exactly as it did twenty years ago.
The machine can still ask the world what time it is.
But it can no longer ask who is online.
In its quiet way, the iBook preserves more than files or applications. It preserves an expectation: that the network would always be there, waiting on the other side of the login window.
The iBook still waits in exactly that way.
Only the network has moved on.